-
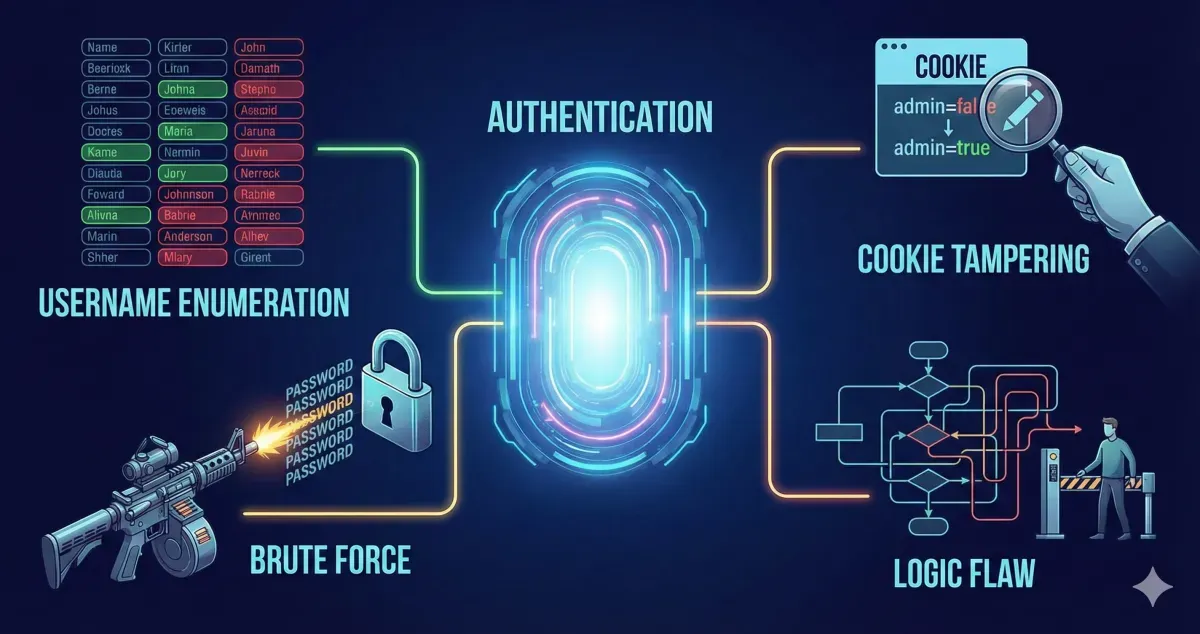 Authentication Bypass | TryHackMe Write-up
Authentication Bypass | TryHackMe Write-upWalktrough for Authentication Bypass TryHackMe room. Learn how to defeat logins and other authentication mechanisms to allow you access to unpermitted areas.
4 min -
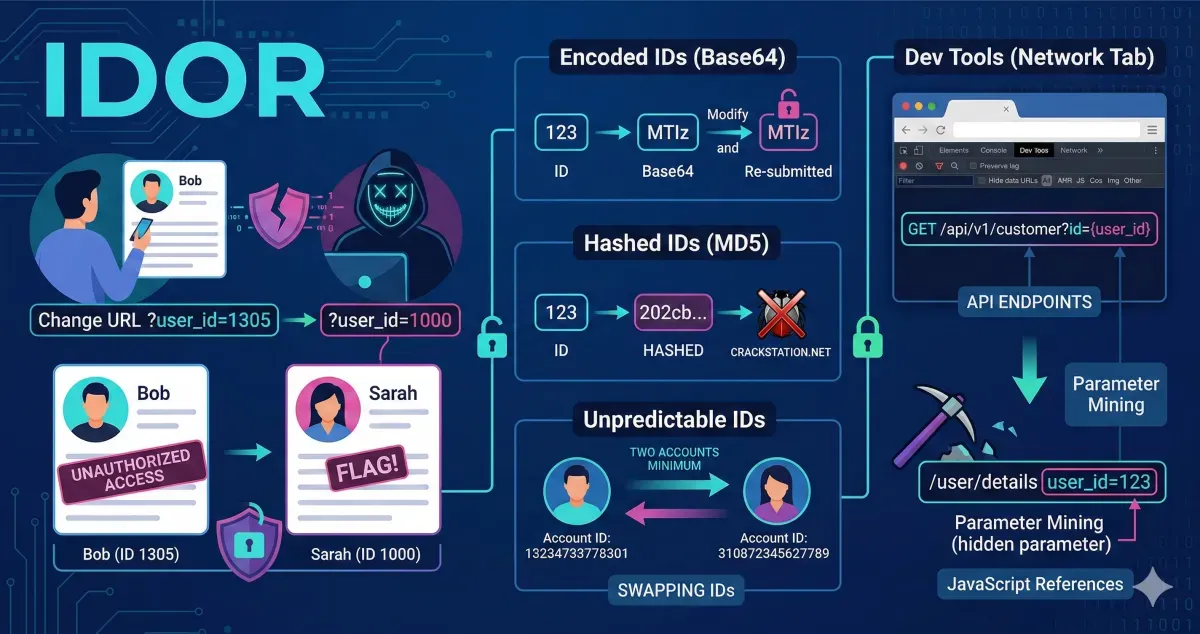 IDOR | TryHackMe Write-up
IDOR | TryHackMe Write-upWalktrough for IDOR TryHackme room. Learn how to find and exploit IDOR vulnerabilities in a web application giving you access to data that you shouldn't have.
3 min -
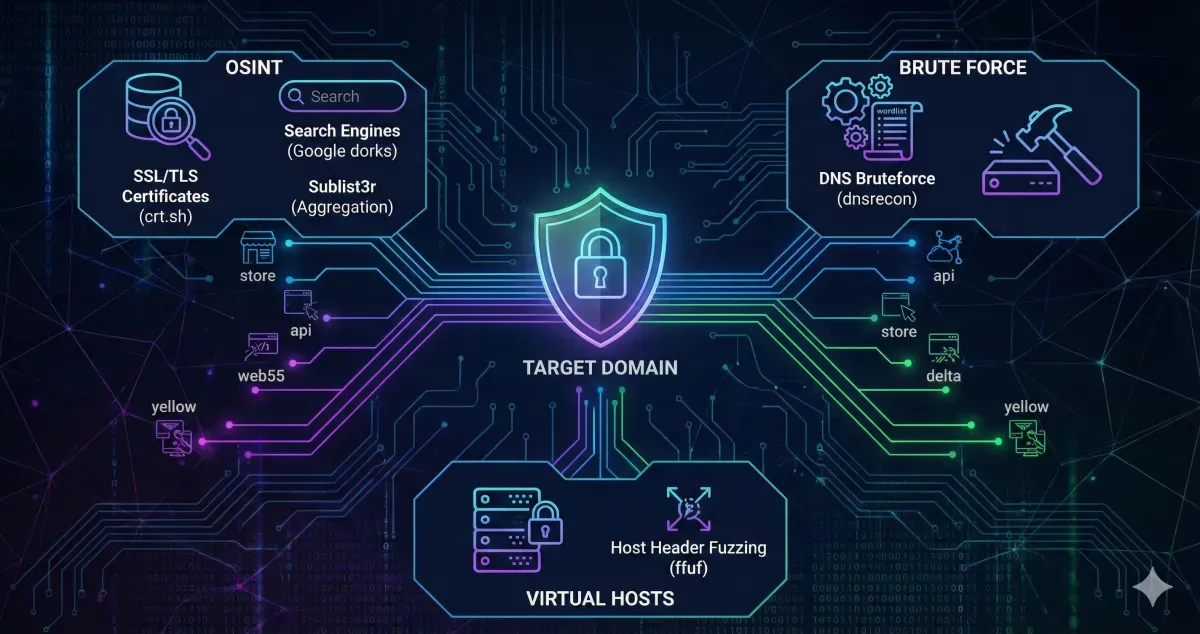 Subdomain Enumeration | TryHackMe Write-up
Subdomain Enumeration | TryHackMe Write-upComplete walktrough for Subdomain Enumeration TryHackme room. Learn the various ways of discovering subdomains to expand your attack surface of a target.
3 min -
 Content Discovery | TryHackMe Write-Up
Content Discovery | TryHackMe Write-UpTryHackMe write-up for “Walking An Application.” Learn how to use browser developer tools to manually discover hidden flags and potential vulnerabilities.
5 min -
 Walking An Application | TryHackMe Write-Up
Walking An Application | TryHackMe Write-UpHands-on walkthrough of Walking An Application on TryHackMe, exploring source code, Inspector, Debugger, and Network tools to uncover hidden flags.
5 min -
 OWASP Top 10 2025: Insecure Data Handling | TryHackMe
OWASP Top 10 2025: Insecure Data Handling | TryHackMeHands-on walkthrough of Cryptographic Failures, Injection, and Integrity Failures in OWASP Top 10 2025 using TryHackMe labs.
3 min -
 OWASP Top 10 2025: Design Flaws | TryHackMe
OWASP Top 10 2025: Design Flaws | TryHackMeLearn about A02, A03, A06, and A10 and how they related to design flaws in the application.
4 min -
 n8n: CVE-2025-68613 | TryHackMe Write-Up
n8n: CVE-2025-68613 | TryHackMe Write-UpLearn how adversaries can exploit the CVE-2025-68613 vulnerability in n8n.
3 min en